With around 32.3%% of all the world’s websites powered by WordPress and Pipe Ten customers choosing WordPress Hosting more and more each day, we’ve put together this post about securing WordPress and keeping your site safe.
Keeping a website secure is becoming more and more important each day. With cyber crime becoming more widespread, you need to ensure you’re taking steps necessary to not become a victim. Always assume you’re a target and capable of being hacked. Make it your job to do what it takes to prevent it from actually happening.
Please Note: This guide uses .htaccess configuration files to help protect your WordPress site. This means this guide’s code based examples should only be used on an Apache web server within your site’s .htaccess file/s.
Update WordPress Core Files, Plugins and Themes
Secure Your Admin Login Page
- Don’t use common usernames such as ‘admin’, ‘administrator’ or ‘wpadmin’.
- Use a secure password.
- Protecting wp-admin/wp-login – Enforcing Rules and IP Blocking
- Limiting Login Attempts
- Enabling 2-Factor-Authentication (2FA)
- Rename the wp-admin Login URL
Protecting your Files and Directories
- Disable Directory Indexes
- Setting the correct File Permissions
- Password Protecting Files and Directories
- Protecting the /wp-content/uploads/ directory
Keeping your Personal/Work Machine Secure
- Ensure you have a good anti-virus software installed
- Wi-Fi Public Networks – Use a VPN
- Using Secure Passwords
- Use Biometrics/Facial Recognition on your Devices
Miscellaneous Security Practices
- Change the Default Database Prefix
- Enforce HTTPS Connections
- Regularly Backup your Site
- Change the Default Secret Keys
- Disable Theme and Plugins Code Editor
- Disabling XML-RPC – Preventing Brute Force Amplification
- Blocking Hotlinking
- Scan Your Site’s Files with WordPress Health Check Plugin’s File Integrity Checker
- Conclusion
Update WordPress Core Files, Plugins and Themes
WordPress is a CMS (content management system) which helps website owners/developers manage the digital content on their website. It works similarly to other pieces of software you may find on your computer. You download it, install it under your hosting account and then begin to use it. Getting started is incredibly simple.
One of the key aspects often forgotten about by the user is maintaining this software. No one is perfect at what they do and everyone is prone to making mistakes. Sometimes developers accidentally leave bugs, loopholes and security vulnerabilities within their code and in order to fix these issues for their software’s users, they often provide patches to download and install to help deal with the problems they may be having.
When it comes to WordPress itself, their developers release updates on a regular basis. It is essential these are installed, especially the security and maintenance patches. It is extremely important that you keep your WordPress installation and core files up to date before anything else.
Plugins and themes for your WordPress websites also need to be kept up to date. Updating them through WordPress is often very simple, however there are sometimes a few things you may need to look out for.
A lot of plugins and themes are developed via third parties and their developers are not linked to WordPress. This can sometimes lead to plugins and themes no longer being supported in future versions of WordPress. It is essential you phase these plugins/themes out and replace them with currently supported alternatives. They can become incredibly insecure as more and more unpatched vulnerabilities are found over time. Any unused plugins/themes should be removed, as, even if disabled, they can succumb to being exploited.
WordPress does offer the ability to automatically update the core of the application, as well as its plugins and themes, if you wish. This is only recommended if you’re certain about the longevity of your plugins and their compatibility with the latest versions of WordPress. In other words, they need to be regularly updated by their developers and you must be confident the plugins/themes aren’t known to usually have many issues when a new version of WordPress is released.
Secure Your Admin Login Page
In terms of people attempting to hack your website, the most common way of them trying to do so is by brute-forcing your admin login page. Brute force attacks are often very simple to execute. The attack often consists of a list of usernames and commonly used/leaked passwords. These are then used in multiple combinations repeatedly until login is successful.
There are a number of ways you can help prevent a brute force attack on your website, a few of which can be found below:
Don’t use common usernames such as ‘admin’, ‘administrator’ or ‘wpadmin’
If you’re using any common or default usernames for your WordPress administrator login, it is highly recommended that you change these ASAP. These usernames are well known in the hacker community to be extremely common. They’re usually put in place as a username by default for the user’s convenience, however they cause more problems than they are worth.
If you’re using a common or easy to guess username, the attacker then only has to guess the password, making things a lot easier for them as they only have to guess one field instead of the two.
Use a secure password
This one speaks for itself really. If you have a weak lock on your house, it’s going to be easier for someone to force their way in. The same goes for having a weak password to gain access to your website. It’ll be much easier for someone to gain unauthorised access if you use a terrible password.
We cover the golden rules for creating a secure password, as well as provide our own secure password generator. Using these to create a password to use will lead to a much more secure website and also help prevent brute force attacks from being incredibly easy to perform.
Protecting wp-admin/wp-login – Enforcing Rules and IP Blocking
By default, WordPress sets your backend login page to wp-admin.php or wp-login.php. This means that anyone browsing your website has access to the login portal used to gain access to the administrative side of your WordPress installation.This page is the one that is most often targeted by people looking to exploit your website, especially when it comes to brute-force attacks.
Luckily, there are numerous ways to protect these pages from attackers, including limiting login attempts, blocking access from certain IP’s, or even password protecting the page from being visited and the wp-admin folder and its contents.
Limiting Login Attempts
The best method for putting in place this form of protection is by installing a plugin that supports the ability to help protect your login page for you.There are sole plugins dedicated to preventing brute-force attacks, however a lot of security related plugins now have the brute-force protection feature built into them.
Enabling 2-Factor-Authentication (2FA)
You can quite easily protect your WordPress login screen using 2FA via a plugin on your site. It would allow you to use the Google Authenticator application or similar on your mobile device to add an extra layer of protection through an OTP (One Time Password). Having 2FA enabled means that, even if a hacker guesses your username and password, they would still require access to your device with the authenticator installed on it to receive the OTP. Without this, they would not be able to log in to your WordPress backend.
Rename the wp-admin Login URL
It is well known the wp-admin login page is accessed via the ‘yourdomain.co.uk/wp-admin’ URL by default on every fresh WordPress installation. This means your login page is incredibly easy to gain access to for attackers if they wish to try and gain unauthorized access. Despite some of the other methods in this part of the guide helping to ensure attackers struggle accessing your login page, you can create security by obscurity by changing the URL used for accessing your administrator login page.
You can change the wp-admin login URL in numerous ways, including using certain plugins (this is the easiest way to do this), however the .htaccess/wp-login.php method is the best option if you do not wish to use a plugin.
1. Locate your wp-login.php file over FTP and copy its contents.
2. Create a file with the same name as what you wish to add onto the end of your login URL. E.g. If I wanted my login page to be visited by the URL mysite.co.uk/lgnpge, I’d create a file called lgnpge.php and paste the wp-login.php code into the file.
3. Open the newly created login file and find and replace all references to wp-login.php with your new .php file’s name (E.g. lgnpge.php).
4. Take a backup of your unaltered wp-login.php file and then delete the one that resides on the server.
5. Access your new login page using the appropriate URL you have set. (E.g. mysite.co.uk/lgnpage.php).
6. It should take you to your admin login page and any visits to yoursite.co.uk/wp-admin or yoursite.co.uk/wp-login should send you to a 404 page.
Protecting your Files and Directories
People don’t always have to be able to login to your WordPress backend to be able to cause some damage. Your files and directories can be prone to abuse if you don’t protect them adequately. This part of the guide will help explain what you can do to ensure your security is hardened when it comes to your site’s files and directories.
Disable Directory Indexes
By default on Apache (Linux Hosting Plans), the ability to browse your site’s directory index and file hierarchy via your browser is enabled. This could cause some security issues, as it allows some of your sub-directories to be explored in a web browser via anyone who types in the correct path in their address bar. An example of what directory indexing looks like can be seen below:
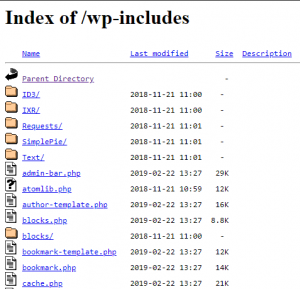
To find out how to disable directory indexes, please follow our separate guide on how to do so.
Setting the correct File Permissions
File permissions are very important for your WordPress site. With the incorrect file permissions, it can cause all sorts of security issues on your site. The easiest way to make sure your file permissions are acceptable is by using your preferred FTP client.
WordPress themselves recommend all of your directories are set to 755 or 750. Files should be 644 or 640 with the exception of the wp-config.php file. This file contains your database connection strings, meaning if someone accessed this file, they’d be able to also access your database using the login credentials within. It is recommended by WordPress that the permissions for the wp-config file on a shared server should be 440 or 400.
Password Protecting Files and Directories
You can use a .htaccess file to password protect certain directories, or even block access completely from certain IP’s or hosts. This increases security greatly, but should be handled with care as you could be locked out of your site if you’re forgetful of passwords or if you have a dynamic IP address from your ISP. It is often recommended to add a .htaccess with the code mentioned above to the /wp-admin/ directory to help harden it and prevent access to files you don’t want to be publicly accessible.
Protecting the /wp-content/uploads/ directory
The WordPress uploads directory can be prone to abuse if left insecure. It has a common tendency to be one of the main places a hacker uploads their malicious scripts in order to gain unauthorised access to your site. They often do this through exploitable themes or plugins on your site, which is another reason why it is so important to keep them updated! A good way to harden this directory is to upload a .htaccess file there containing the following code:
<Files *.php> Require all denied </FilesMatch>
This code will block all access to .php files uploaded to the directory the .htaccess is placed in, meaning that it is unexecutable and frankly unusable by the attacker.
Please note: You can also place this in a .htaccess within your wp-includes directory, however you may need to check whether your plugins still work as expected upon using the above code before pushing the change live.
Keeping your Personal/Work Machine Secure
One of the biggest overlooks in security sometimes comes down to bad security practices on the end-user level. Below you’ll find a few examples of better ways to ensure your device’s are secure from an end-user perspective.
Ensure you have a good anti-virus software installed
Putting some form of local antivirus software on your devices will be incredibly useful. A common way for hackers to gain access to your passwords is by tricking you into installing malicious software onto your computer. They can easily log every keystroke you make if they wish once this has been installed. An antivirus solution will help scan your computer for any signs of infected files, quarantining and removing the issue if they find anything they see as a potential risk or threat. Some solutions also notify you if you’re in the process of downloading a malicious file, which is extremely useful in order to prevent it from infecting your system. This could come in handy when managing local instances of your site, or when downloading third party themes or plugins that claim to be ‘free and premium’ to manually install on your site.
Wi-Fi Public Networks – Use a VPN
With free to the public Wi-Fi services being offered by more and more companies, this means there are more and more ways a hacker can gain access to information on your device. A lot of the Wi-Fi networks put in place in restaurants, hotels and airports are completely accessible to anyone, meaning anyone can connect without issue. If an attacker connects to the network, they can most likely capture network traffic and see everything you do, including what passwords you’re typing in and where if they look hard enough. The best way to counter this is to try and avoid connecting to public Wi-Fi when possible.
If you need to access public Wi-Fi, it is recommended you use a VPN service on your device to help encrypt network traffic so that it’s unreadable if intercepted. We offer a free VPN service to use if you’re one of our customers, which is great for encapsulating communications between your computer and Pipe Ten’s services.
Using Secure Passwords
Creating a secure password is a high priority when using any software/device that requires them. As soon as someone has access to these passwords, they also have automatic access to whatever you use them for. Your FTP password is one of the most important when it comes to protecting your WordPress site. If you have your WordPress site linked up to a mailbox too, the password for this will also need to be secure.
Consequences of having a weak password include the possibility of it being brute forced and just having your password guessed outright. Hackers won’t even need to gain access to your password illegitimately if they manage to just guess it. Don’t make things easier for them!
Use Biometrics/Facial Recognition on your Devices
Over the years, the technology industry has seen the introduction of biometrics and facial recognition on devices such as mobile phones and laptops. Before these were available, users had to rely on passcodes or simple patterns to keep their devices secure, which simply weren’t secure enough. These passcodes/patterns were often easy to guess, which lead to a lot of people being able to gain unauthorised access to a device. Now that mobile phones contain so much of our personal information, such as payment details and emails, we need to keep these much more secure. Although not completely foolproof, having biometrics/facial recognition on a device is much more secure than using a passcode/pattern.
Miscellaneous Security Practices
This section will cover methods you can use to harden WordPress that are more specific to an area outside of the above mentioned ones.
Change the Default Database Prefix
Database prefixes are used to help avoid name conflicts and identify tables when there are multiple applications using the same database. By default, WordPress sets these prefixes to wp_, leaving your site vulnerable to your table names being guessed. This makes attacks such as SQL Injection a lot easier to perform, where the attacker injects SQL syntax into an input field on your site in hopes it’s linked to your database to execute a query. If successful, they could list the entire contents of one of your database’s tables, such as one that is used to store account usernames or email addresses, or they could even inject their own user into the database and use it to login as an administrator to the backend of your site.
You obviously want to avoid this, so you’ll need to ensure when installing WordPress that you specify a unique database prefix. You can input this at step 3 of our WordPress installation guide.
If you already have an active WordPress installation using the default DB prefix, you can always change this manually, but you would be best speaking to your web developer about this if you’re not comfortable doing it yourself. It can be done using phpMyAdmin or a similar application with simple SQL query capabilities.
Enforce HTTPS Connections
The traffic on your website between the end-user and the server is sent over HTTP (Hyper-Text-Transfer-Protocol) by default, which is known to be an insecure way to transport data over the internet. The recommended protocol to ensure security standards are met is HTTPS (Hyper-Text-Transfer-Protocol-Secure), which ensures all communication between your web browser of choice and the server your site is hosted on is encrypted using TLS (Transport Layer Security), or its predecessor, SSL (Secure-Sockets-Layer).
This form of connection can be enabled by installing an SSL certificate on the server your website is hosted on. This allows the server to help encrypt and decrypt traffic as it travels across the internet to and from your web browser, meaning during that transportation, no one can decrypt the data you send and access any information within without the private key. This is incredibly useful for protecting information such as credit card details, login credentials, customer addresses and so on. We offer both unmanaged and fully managed SSL’s, which means you can either install them yourself, or we can install them for you.
Please Note: You will need to enforce HTTPS connections within your .htaccess file once HTTPS connections are enabled to make sure no users are able to connect over HTTP still.
Regularly Backup your Site
It is incredibly important that you backup your WordPress site on a regular basis. If your site gets hacked and infected with malicious code, especially one that has a tendency to spread, you’ll need to deal with this quickly and efficiently and quarantine it. Removing the site’s infected files from the server is often the only way of doing this, but in turn, irreparable damage will have potentially been done to your site. This is where a backup of your site before the compromise could be incredibly useful.
We do take backups of our shared services on a regular basis, and are more than happy to restore your site’s files or database if you wish. Despite this, we still highly recommend that customers take their own backups and ensure it is in their best interests to do so. There are many plugins for WordPress which you can use to backup your entire site and its database in a few clicks, as well as restore it upon install of a fresh WordPress instance if your old site was riddled with issues after a compromise.
Change the Default Secret Keys
Change the following code within your wp-config.php using the secret key generator below.
define('AUTH_KEY', '');
define('SECURE_AUTH_KEY', '');
define('LOGGED_IN_KEY', '');
define('NONCE_KEY', '');
Visit WordPress’ own key generator and copy and replace your code with the generated one. This is vital for salt, which will help keep the hashing of your sensitive data secure.
Disable Theme and Plugins Code Editor
If your wp-admin credentials are compromised and a malicious user has gained access to the backend of your site, it is highly likely they’re going to have a click around and cause as much damage for their own gain as they possibly can. One thing they are capable of doing is editing your themes and plugins files via WordPress’ built-in code editor if the unknowing user hasn’t disabled the ability to do this.
You can help avoid attackers from inputting hidden malicious code into your themes and plugins by adding the following code to your wp-config file:
define( 'DISALLOW_FILE_EDIT', true );
This will disable the theme and plugin code editor you can use within WordPress’ backend, meaning the attacker will need to use other means to hide malicious code in your important files.
Disabling XML-RPC – Preventing Brute Force Amplification
XML-RPC (Extensible Markup Language – Remote Procedure Call) is an RPC protocol which can be encoded using XML and which uses the HTTP protocol as a transportation method across a network.
The risk involved with using XML-RPC on your WordPress site includes the system.multicall method, which is a feature that allows the execution of multiple commands within a single HTTP request. Usually, a brute force attack would consist of multiple HTTP requests and each username/password check would be done individually. This is usually easy to spot and defend against using logging, limited login attempts and IP blocking thanks to the multiple requests showing an obvious, detectable pattern.
Using the XML-RPC method to perform the attack would allow these username/password checks to be done in a singular HTTP request, all thanks to the multiple commands within the request being executed all at once. An attacker can perform hundreds of password checks using this method in just one attempt, which will appear in your logs as just a singular entry. This is a lot more difficult to spot when compared to the multiple entries you’ll see in traditional brute force attacks. When put into layman’s terms, this method could be seen as the attacker launching a large nuke at your website, rather than launching multiple smaller missiles that are much more manageable and easier to deal with.
If you’re not making use of XML-RPC, it is highly recommended that you disable it. You will need to check whether your site makes use of it before disabling it’s capabilities, as it can cause issues with certain plugins.
The best method to disable XML-RPC is using your site’s root .htaccess to block any requests made to the xmlrpc.php file using the code shown below:
<Files xmlrpc.php> Require all denied </Files>
Blocking Hotlinking
Hotlinking can be used to grab an image from anywhere on the internet and show it on a site by using the image’s current URL. The exact URL will be referencing the original images location, which means it’ll be served from an external source to the hotlinking site from wherever the image is located. The most likely source would be other people’s websites.
Despite this sounding convenient for the person performing the hotlinking and it seeming harmless, it actually comes with a lot of issues. For example, if you’re hotlinking to copyrighted content, it could become a legal matter. The hotlinking also uses up the resources where the content is originally served from, so you could inadvertently be increasing traffic to the server where the hotlinked image is located on, potentially causing huge issues for whoever the image is sourced from.
The best way to prevent people from hotlinking your own images so you don’t run into these problems is to add some code to your .htaccess file.
RewriteEngine on
#Allow Blank Referrers
RewriteCond %{HTTP_REFERER} !^$
#Allow your site to link to media directly
RewriteCond %{HTTP_REFERER} !^http(s)?://(www\.)?yourdomain.co.uk [NC]
#Allow search engines to show your images in search results
RewriteCond %{HTTP_REFERER} !^http(s)?://(www\.)?google.com [NC]
RewriteCond %{HTTP_REFERER} !^http(s)?://(www\.)?bing.com [NC]
RewriteCond %{HTTP_REFERER} !^http(s)?://(www\.)?yahoo.com [NC]
#Add this to show an image in place of the hotlinked media
RewriteRule \.(jpg|jpeg|png|gif|svg)$ http://www.yourdomain.co.uk/nohotlinking.png [R,NC]
Scan Your Site’s Files with WordPress Health Check Plugin’s File Integrity Checker
WordPress sites are made up of a lot of files, so it would be a pain to search through them all to find any malicious code that may be left over after a compromise. The File Integrity Checker tool built into the WordPress Health Check plugin helps perform this job for you.
This tool is incredibly useful when you believe you have a compromised site.
The core files of WordPress have their own unique checksums (a sequence of numbers and letters) that are calculated via complex algorithms. The WordPress API will provide these checksums to compare to your own site’s core files. If the calculated checksum of your files are different to the API’s, it will notify you and allow you to perform a diff check to see what the text based differences are. This is useful for spotting any malicious code an attacker has tried to hide within your site’s core files that you were previously unaware of.
We have a guide which helps explain how to use this tool, as well as other useful features included within the plugin.
Conclusion
In conclusion, it is essential to keep your WordPress installation secure to ensure no harm comes to your site or its visitors. Here at Pipe Ten, we take security very seriously, so helping customers keep their websites secure is at the top of our priorities list.
There are four main points to stick to when it comes to WordPress security, with some of these being applicable to other applications as well:
- Update Everything. This will ensure any vulnerabilities are dealt with that would otherwise leave huge security holes present.
- Reinforce your Login Pages. If someone was to gain backend administrative access to your site, they can pretty much take full control of its configuration and all of the content present.
- Protect your Files and Directories. Your files and directories are prone to being abused and have the possibility of being publicly accessible to anyone on the internet upon a fresh WordPress install. Locking these down is a must, especially if you have sensitive files on the server and want to keep your visitor’s safe.
- Secure your local machine. This is absolutely vital if you’re managing your website remotely using multiple devices. Your website’s security will mean nothing to those who have full access to it through your personal devices thanks to keyloggers and more.
Following the advice above should get you to where you need to be when it comes to keeping your WordPress site secure. If you believe your site has been compromised, please read our guide on what to do next and feel free to get in touch with us if you have any questions.

Classification: Public
Last saved: 2024/04/19 at 15:17 by Gavin
